開源日報 每天推薦一個 GitHub 優質開源項目和一篇精選英文科技或編程文章原文,堅持閱讀《開源日報》,保持每日學習的好習慣。
今日推薦開源項目:《應用級JS語言 TypeScript》
今日推薦英文原文:《Security Questions Are a Terrible, Horrible, Bad Idea》
今日推薦開源項目:《應用級JS語言 TypeScript》傳送門:GitHub鏈接
推薦理由:TypeScript是一種應用級JavaScript語言。TypeScript為JavaScript添加了可選的類型,支持針對任何瀏覽器、任何主機、任何操作系統的大型JavaScript應用程序的工具。TypeScript編譯成可讀的、基於標準的JavaScript。
今日推薦英文原文:《Security Questions Are a Terrible, Horrible, Bad Idea》作者: Meriam Kharbat
原文鏈接:https://medium.com/better-programming/security-questions-are-a-terrible-horrible-bad-idea-da108e303240
推薦理由:還記得你的中學老師么?很可能上一次被問到這個問題是你在某個賬戶填寫密保的時候。但是這種安全問題其實很不靠譜,很糟糕。
Security Questions Are a Terrible, Horrible, Bad Idea
Stop asking me for my mother』s maiden name
(Photo by vardan harutyunyan on Unsplash)
As I was setting up my account at Deutsche Bahn, I was surprised to see the following UI:
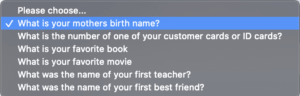
(Deutsche Bahn account UI)
After the 2013 Yahoo security breach that compromised 3 billion user accounts, it should be common knowledge by now that security questions are a terrible idea. Why are they still a thing?
They Can Be Very Easily Guessed
The main idea behind security questions is they』re safe and memorable. But with today』s social media, anyone can scroll over my posts and figure out the name of my high school mascot, and if I can remember it, then probably a lot of people can too.
This 2015 Google study has confirmed that with only a single guess, an attacker would have a 19.7% chance of guessing an English-speaking user』s answer to the question 「What is your favorite food?」.
With 10 guesses, an attacker would have a 24% chance of figuring out Arabic-speaking user』s answer to the question: 「What was your first teacher』s name?」 and a 39% chance of guessing a Korean-speaking user』s city of birth (and a 43% chance of guessing their favorite food).
Many different users also had identical answers to secret questions you』d typically expect to be unique, such as 「What』s your phone number?」 or 「What』s your frequent flyer number?」.
Then, 37% of people deliberately provide false answers to their questions, thinking this would make them harder to guess, when, in fact, it made it even easier to figure out.
They Can Be Brute-Forced
We demand a user enters a password that contains lowercase and uppercase letters, numbers, and special characters.
But we hide the account recovery mechanism behind a silly question that can be brute-forced? This doesn』t make any sense to me!
They Make Wrong Assumptions About Your Users
Maybe in the Western world, people can find security questions relatable. But I didn』t have a pet, I』m not good at remembering people』s names, and I was never married, so I never went on honeymoon.
Growing up in North Africa, I didn』t even know what a maiden name meant because where I come from, women don't take their husband's names.
So that left me with what』s your favorite dish, and anyone who knows me can guess what that is.
That』s a terrible user experience that excludes anyone who isn't from the same cultural background as the person who developed the application. By doing so, we compromise their privacy because we narrow the questions that they might find relatable.
Conclusion
Today, many available services make authentication integration seamless.
Please implement a proper two-factor authentication flow instead of compromising your users』 privacy.
And next time someone asks me what my favorite dish is, it』ll be something like cOüs;Coū!68$!
下載開源日報APP:https://openingsource.org/2579/
加入我們:https://openingsource.org/about/join/
關注我們:https://openingsource.org/about/love/
The main idea behind security questions is they』re safe and memorable. But with today』s social media, anyone can scroll over my posts and figure out the name of my high school mascot, and if I can remember it, then probably a lot of people can too.
This 2015 Google study has confirmed that with only a single guess, an attacker would have a 19.7% chance of guessing an English-speaking user』s answer to the question 「What is your favorite food?」.
With 10 guesses, an attacker would have a 24% chance of figuring out Arabic-speaking user』s answer to the question: 「What was your first teacher』s name?」 and a 39% chance of guessing a Korean-speaking user』s city of birth (and a 43% chance of guessing their favorite food).
Many different users also had identical answers to secret questions you』d typically expect to be unique, such as 「What』s your phone number?」 or 「What』s your frequent flyer number?」.
Then, 37% of people deliberately provide false answers to their questions, thinking this would make them harder to guess, when, in fact, it made it even easier to figure out.
They Can Be Brute-Forced
We demand a user enters a password that contains lowercase and uppercase letters, numbers, and special characters.
But we hide the account recovery mechanism behind a silly question that can be brute-forced? This doesn』t make any sense to me!
They Make Wrong Assumptions About Your Users
Maybe in the Western world, people can find security questions relatable. But I didn』t have a pet, I』m not good at remembering people』s names, and I was never married, so I never went on honeymoon.
Growing up in North Africa, I didn』t even know what a maiden name meant because where I come from, women don't take their husband's names.
So that left me with what』s your favorite dish, and anyone who knows me can guess what that is.
That』s a terrible user experience that excludes anyone who isn't from the same cultural background as the person who developed the application. By doing so, we compromise their privacy because we narrow the questions that they might find relatable.
Conclusion
Today, many available services make authentication integration seamless.
Please implement a proper two-factor authentication flow instead of compromising your users』 privacy.
And next time someone asks me what my favorite dish is, it』ll be something like cOüs;Coū!68$!
下載開源日報APP:https://openingsource.org/2579/
加入我們:https://openingsource.org/about/join/
關注我們:https://openingsource.org/about/love/
